An estimated 7.7 GB of data has been stolen from the computers and mobile phones of anti-regime fighters in Syria, a new study has revealed.
Sexual entrapment has become a dominant pillar of cyber warfare launched by President Assad's regime. Syrian opposition and rebel fighters have been subjected to piracy and hacking. Stolen data includes military and political information, humanitarian activities, refugees profiles, communication and media. The material has been obtained by hackers, posing as seductive women, to entice military secrets from the fighters through the use of malware.
The revelations are detailed by FireEye, a private company that provides cyber-security solutions to governments and corporations. Its special report “Behind The Syrian Conflict's Digital Front Lines” [pdf], focuses on the Syrian regime's sex-based hacking operations:
We uncovered these battle plans in the course of our ongoing threat research. It quickly became apparent that we had come across stolen documents containing the secret communications and plans of Syrian opposition forces that had fallen victim to a well-executed hacking operation.
Seduction and sex as weapon is as old as the story of Delilah, when she seduced the powerful Samson. “Delilahs” in 21st century are Pro-Assad hackers who have tricked Syria's rebels (possibly, some from ISIS) into falling for the oldest scam on the Internet in chats with “girls”. The hackers establish contact with fighters via Skype, pretending to be an attractive woman. They then send an image malware – tailored to PC or smartphone – which automatically establishes a remote-access tool known as DarkComet, embedded in their sexy selfies.
On its report, on page 12, FireEye reports a representative chat between IMAN (hacker) and her target (victim):
IMAN: How are you on skype? On a computer or on your phone?
TARGET:How are you?
IMAN: Are you opening Skype on your mobile?
TARGET: Computer and mobile
TARGET: How old are you?
IMAN: 25
IMAN: And you?
TARGET: What is your date of birth?
IMAN: 10-3-88
TARGET: Lololol
TARGET: 10-3-89
IMAN: What a nice coincidence
IMAN: Sent file New-Iman-Picture.pif
TARGET: You drive me crazy
Iman and the victim sharing the same date of birth is no coincidence. The fighter’s birthday is available on Skype and social networking sites, information the hackers already have.
AnonymousHQ comments on the reported cyber incidents on its website:
It is not yet clear whether the hackers have passed the stolen information of the Syrian rebels to the Syrian government or not. If the stolen information is passed on to the Syrian government, it would help them in defeating the rebels. We don’t have any information regarding the hackers behind this operation.
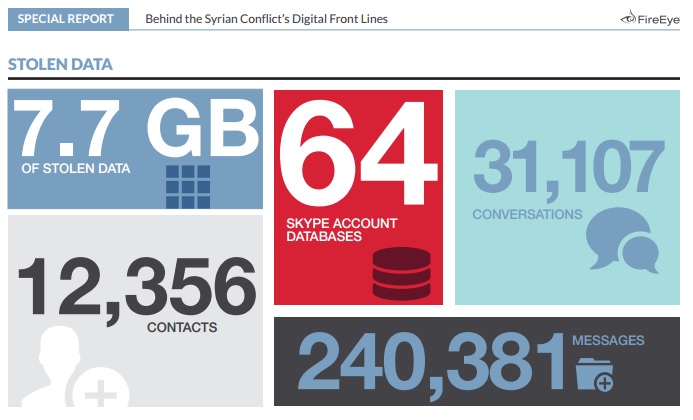
Screenshot of the FireEye report.
7.7GB of Data Stolen
According to the report, these hacking actions resulted in 7.7 GB of stolen data, including military and political information, humanitarian activities, refugees profiles, communication and media. It says 64 Skype account databases, 31,107 conversations, 12,356 contacts and 240,381 messages have been compromised.
In an Arabic post on Raseef22 blog, Mohamad Ghazi writes about previous sex scandals top anti-regime officers have been embroiled in recently. The article outlines, in detail, how several officers of armed Syrian rebels have become victims of sex hackers, who later on published their “virtual” encounters, including their photographs in compromising positions and videos of their sexual acts, to blackmail them. It explains how the officers fell from grace, and disappeared from public life.
This is not the first time that an international organization exposed how the Syrian regime tends to spy on its opposition. In December 2012, when the Internet was back in Syria after three days of a blackout, the Electronic Frontier Foundation (EFF) reported that it detected two new campaigns of malware targeting Syrian activists associated with the same IP address.
The last report by FireEye comes after 47 weeks of a violent war between fragmented armed divisions opposing the Assad regime who still denies any human rights violations and yet continues to bomb civilian targets despite international condemnation. The war that has killed 210,000 Syrians since March 18, 2011, could now be dictated by information obtained through cyber sex.







7 comments